Manufacturing
Equip to Protect IP
Manufacturing companies were identified as the most susceptible to cyber threats, with bad actors targeting IP and technical trade secrets to then be sold to competitors or nation-states. The majority of manufacturers are classified as small or medium-sized and especially at risk as they often lack in-house resources to defend against sophisticated attackers.
LanScope Cat helps manufacturers address this critical gap in resources by delivering a complete endpoint management product built with AI and automated processes to help short-handed IT teams streamline operations and eliminate hands-on activity to speed response to potential attacks.
Automated
Manufacturer IT teams gain the edge with AI that identifies and prevents malware and memory-based attacks on online or offline endpoints by automatically recognizing devices, and regular scanning to ensure that all endpoints are fortified with the latest agents.

Easy to Use
Provides automatic detection of USB activity, supports remote configuration with simple management of power saving, streamlines asset and device management, and instantly updates repositories and synchronizes software versions – allowing stretched IT teams to redirect on other critical issues.

Streamlined
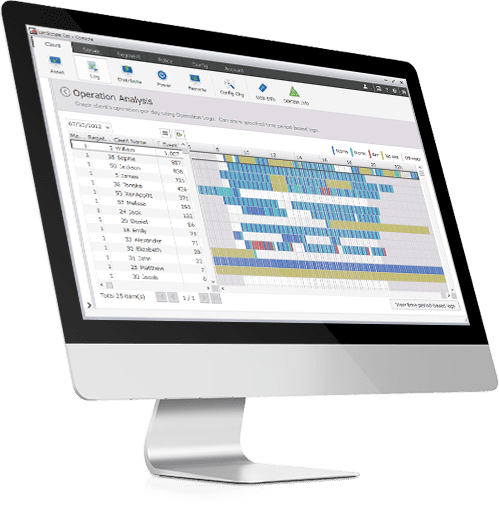
Centralize and organize endpoint management through a single console that consolidates desktops, laptops, and thin clients scattered across multiple shop floors, distribution sites or design locations, while empowering teams with a real-time dashboard that shows at a glance the extent of a threat and if endpoints are infected.
CASE STUDY
Manufacturer Ensures Regulatory Compliance
The Struggle
A defense manufacturer managing 300+ workstations and remote workers’ laptops struggled to ensure ITAR compliance and maintain the balance between productivity and security. Their worst fears were realized when they became aware of content breaches.
The Solution
With file access and USB use compromising compliance, it was essential to quickly address these ITAR compliance risks. LanScope Cat was installed to affordably provided the capabilities needed to rapidly control and monitor file access and mitigate the risks.
The Result
Providing clear visibility across the network, Interfocus audit and usage reports ensure ITAR compliance is maintained. And the client now has a way to easily enforce company policies regarding USB usage. Using LanScope Cat, our client can effectively balance productivity and security.
View. Manage. Protect.
Are You Doing Enough For Security?
Protect & Manage Your IT Before It Gets Out of Control
As your company grows, so do the number of endpoints you have to protect. Did you know over 61% of small businesses experienced a cyber attack in 2016? Hackers see small businesses as easy targets. LanScope Cat changes that.
LanScope Cat protects every single endpoint on your network by allowing you to define and enforce your own company policy. Our easy-to-use console allows you to monitor web activity, external device usage, USB usage, printing activity and more!
Asset Management
Get greater visibility into your assets and how users actually use them. Continual logging gives you a complete picture of the state of your network and what is happening to your data. Establish and enforce policies. Verify system updates and patches have been installed. Track license inventory and usage.
Employee Monitoring
Understand what kinds of activities are actually taking place within your environment and determine patterns of intentional or accidental use. Address serious violations when they occur, through clear and comprehensive activity logs.
Web Access Monitoring
See which users are accessing which websites and for how long. Block access to unauthorized websites and prevent users from accessing restricted URLs and keywords.
USB/External Device Management
Automatically detect USB activity, including usage and idle time, to obtain an instant update of all peripheral activity. Manage remote users and devices to ensure policy compliance and security.
Malware Protection with Cylance
Identify and prevent known and unknown malware and memory-based attacks on online or offline endpoints. LanScope Cat regularly scans every network device to ensure all endpoints are fortified with the latest agents. The dashboard shows files that were detected and quarantined.