Gain Insight with Employee Monitoring
 Know what’s really happening on your network
Know what’s really happening on your network
Do you know how, when and where your employees are using their devices? Employee monitoring with LanScope Cat provides information to help you set policies and guidelines that can help you ensure data security and avoid risky behaviors and activities.
Solve the Problem of User Activity Monitoring with LanScope Cat

 Know what’s really happening on your network
Know what’s really happening on your network Monitor USB Usage
Monitor USB Usage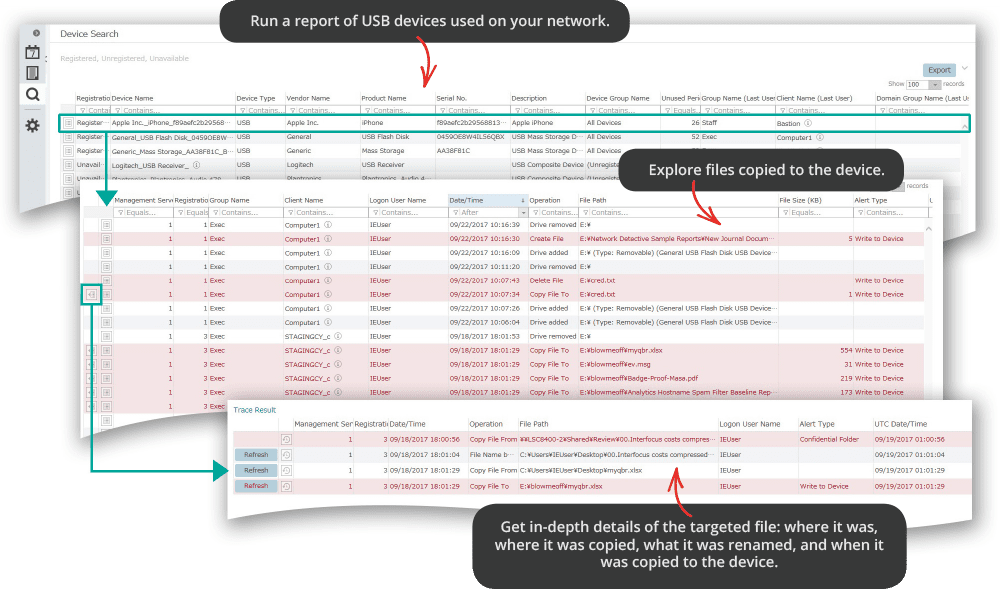
 Monitor Employee Print Usage
Monitor Employee Print Usage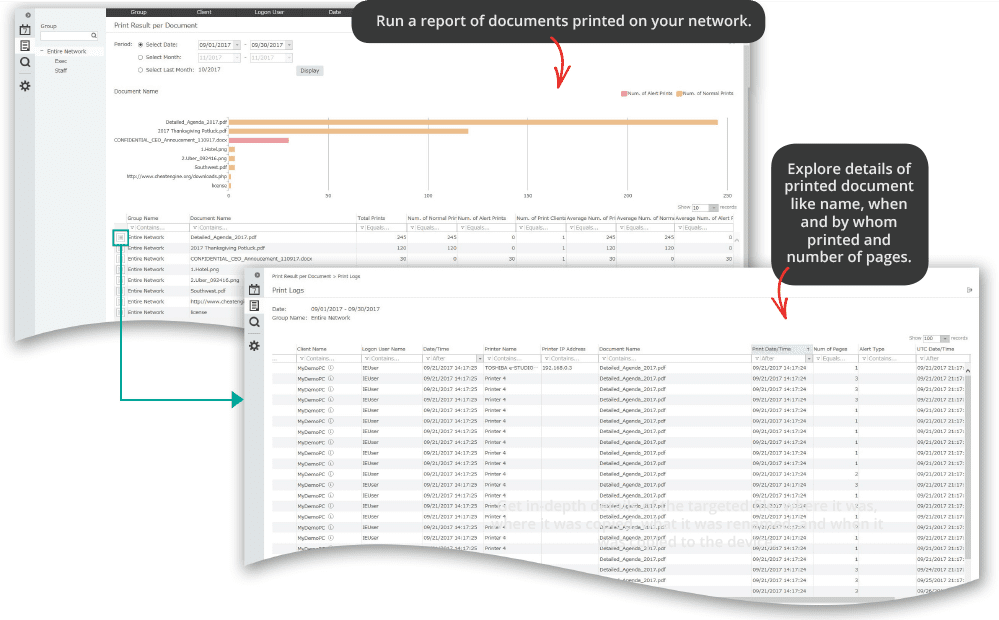
 Monitor Employee Website Access
Monitor Employee Website Access Monitor File Activity
Monitor File Activity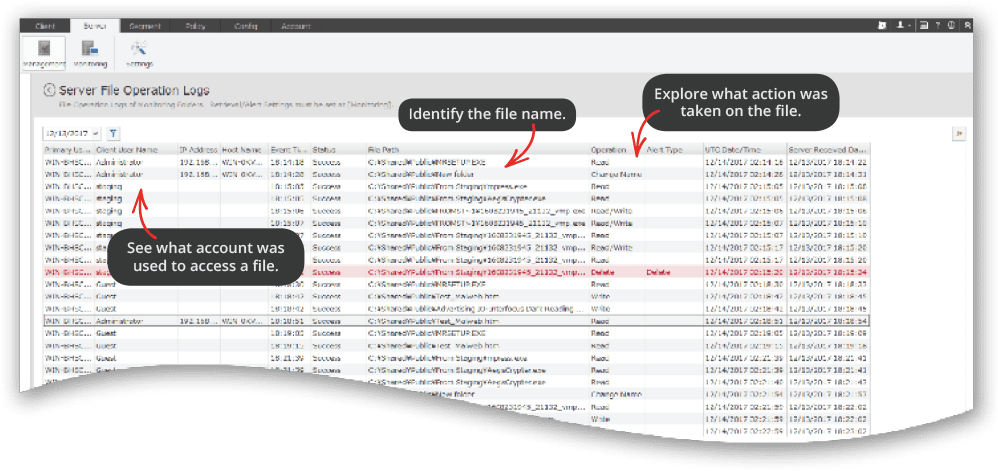
 Monitor Email Usage
Monitor Email Usage



